
Secure Shell (SSH) is often essential for providing an encrypted channel over the Internet and as such is used in many web applications. Yet despite this, many developers do not know much about it. This is a problem because with just a couple of tricks you can save a lot of time and energy.
Learn this popular cryptographic network protocol and become much more efficient in its use with this quick SSH tutorial.
Table of Contents view
What is SSH
SSH, or Secure Shell, is a remote administration protocol that allows users to control and modify their remote servers over the Internet. The service was created as a secure replacement for unencrypted Telnet and uses cryptographic techniques to ensure that all communication to and from the remote server is done in an encrypted manner. It provides a mechanism for authenticating a remote user, transferring input from the client to the host, and forwarding output to the client.
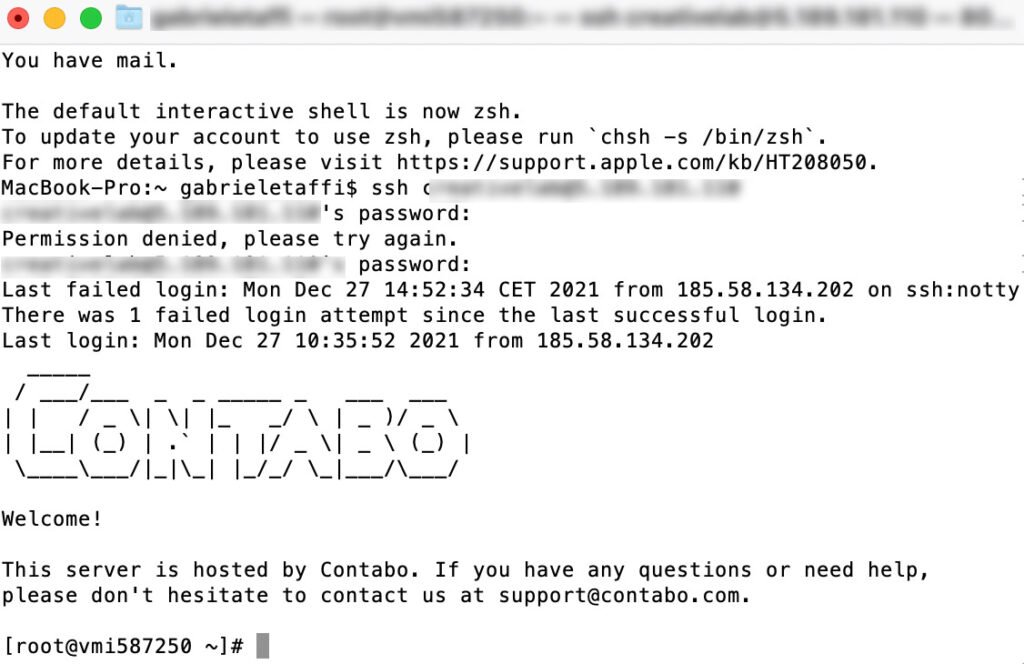
The figure below shows a typical SSH window. Any Linux or macOS user can log in via SSH to their remote server directly from the terminal window. Windows users can take advantage of SSH clients such as Putty . You can execute shell commands in the same way you would if you were physically operating on the remote computer.
This SSH tutorial will cover the basics of how ssh works, including the technologies used by the protocol to provide a secure method of remote access. It will cover the different layers and types of encryption used, along with the purpose of each layer.
How does SSH work?
If you are using Linux or Mac, using SSH is very simple. If you are using Windows, you will need to use an SSH client to open SSH connections. The most popular SSH client for Windows is PuTTY.
For Mac and Linux users, go to your terminal program and then follow the steps below:
The SSH command has 3 distinct parts:
ssh {user}@{host}
The SSH key command tells the system that you want to open an encrypted Secure Shell connection. {user} represents the account you want to access. For example, you may want to access the root user , which is basically synonymous with the system administrator with full rights to modify anything on the system. {host} refers to the computer you want to access. It can be an IP address (e.g., 244.235.23.19) or a domain name (e.g., www.miodominio.com).
When you press enter, you will be asked to enter the password for the requested account. When you type it in, nothing will appear on the screen, but your password is, in effect, broadcast. Once you have finished typing, press enter again. If your password is correct, you will be greeted with a remote terminal window.
Understanding the different SSH encryption techniques.
The significant advantage offered by SSH over its predecessors is the use of encryption to ensure the secure transfer of information between the host and the client. Host refers to the remote server you are trying to access, while the client is the computer you are using to access the host. There are three different encryption technologies used by SSH:
1.Symmetric encryption
2.Asymmetric encryption
3.Hashing.
Symmetric Cryptography
Symmetric encryption is a form of encryption in which a secret key is used for both encrypting and decrypting a message from both the client and the host. In effect, anyone who possesses the key can decrypt the message being transferred.
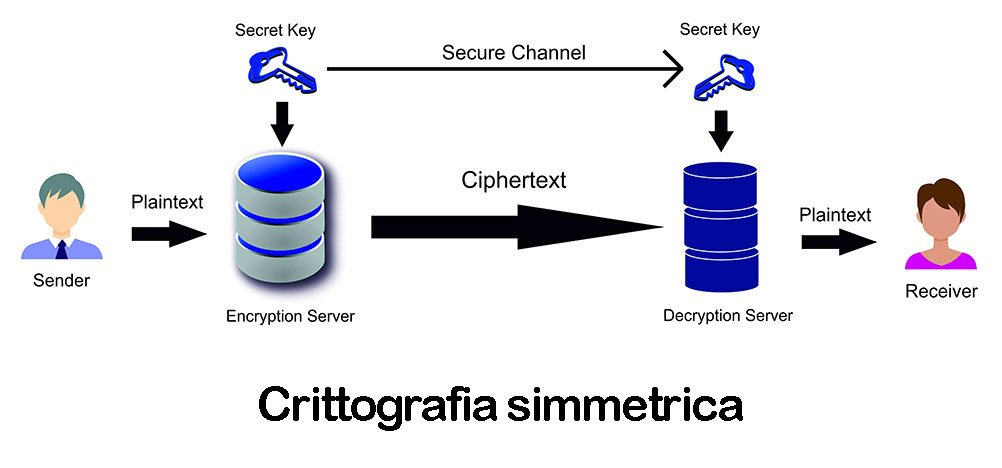
Symmetric cryptography is often called shared key or shared secret cryptography . Usually only one key or sometimes a key pair is used where one key can be easily computed using the other key.
Symmetric keys are used to encrypt the entire communication during an SSH session. Both client and server derive the secret key using an agreed method, and the resulting key is never disclosed to third parties. The process of creating a symmetric key is performed by a key exchange algorithm . What makes this algorithm particularly secure is the fact that the key is never transmitted between the client and the host. Instead, the two computers share public data and then manipulate it to independently compute the secret key. Even if another machine acquires the publicly shared data, it will not be able to compute the key because the key exchange algorithm is unknown.
It should be noted, however, that the secret token is specific to each SSH session and is generated prior to client authentication. Once the key has been generated, all packets moving between the two machines must be encrypted by the private key. This includes the password typed into the console by the user, so credentials are always protected from network packet sniffers.
There are a variety of symmetric encryption ciphers, including but not limited to AES (Advanced Encryption Standard), CAST128, Blowfish, etc. Before establishing a secure connection, the client and a host decide which cipher to use by publishing a list of supported ciphers in order of preference. The preferred encryption among those supported by the clients that is on the host’s list is used as the two-way encryption.
For example, if two Ubuntu 14.04 LTS machines communicate with each other over SSH, they will use aes128-ctr as the default cipher.
Asymmetric encryption
Unlike symmetric encryption, asymmetric encryption uses two separate keys for encryption and decryption. These two keys are known as the public key and private key . Together, both of these keys form a public-private key pair .
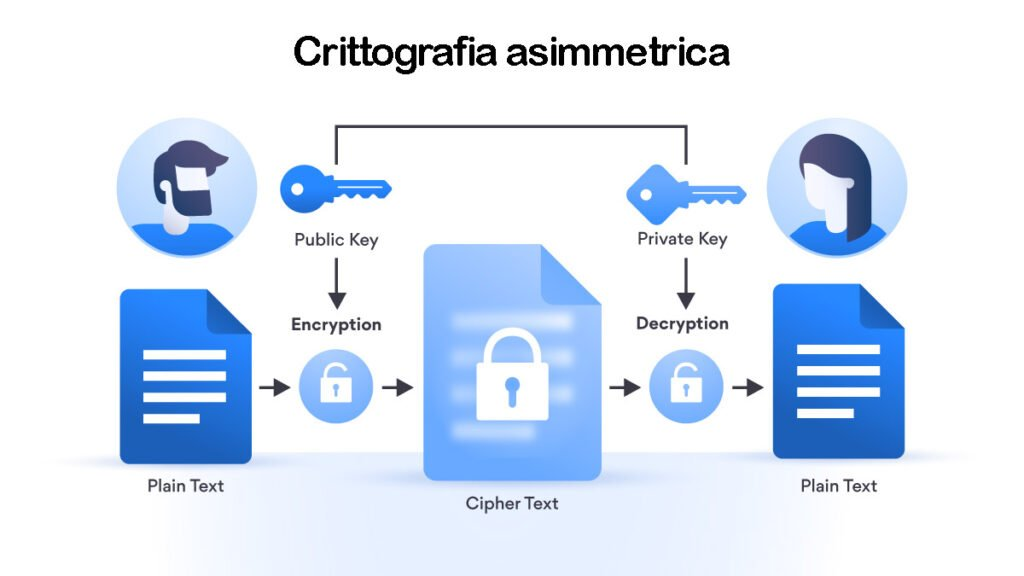
The public key, as the name suggests, is openly distributed and shared with all parties. Although it is closely related to the private key in terms of functionality, the private key cannot be mathematically computed from the public key. The relationship between the two keys is very complex: a message encrypted with the public key of a machine can only be decrypted by the private key of the same machine. This one-way relationship means that the public key cannot decrypt its own messages, nor can it decrypt anything encrypted by the private key.
The private key must remain private, that is, for the connection to be protected, no third party must know it. The strength of the entire connection lies in the fact that the private key is never revealed, as it is the only component that can decrypt messages that have been encrypted using its own public key. Therefore, any party with the ability to decrypt publicly signed messages must possess the corresponding private key.
Unlike the general perception, asymmetric encryption is not used to encrypt the entire SSH session but is used only during the symmetric encryption key exchange algorithm. Before initiating a secure connection, both parties generate temporary public-private key pairs and share their respective private keys to produce the shared secret key.
Once a protected symmetric communication is established, the server uses the client’s public key to generate it, verify it, and transmit it to the client for authentication. If the client successfully decrypts the message, it means it has the required private key for the connection. Then the SSH session begins.
Hashing
One-way hashing is another form of encryption used in Secure Shell connections. One-way hashing functions differ from the previous two forms of encryption in the sense that they are never intended to be decrypted. They generate a unique value of fixed length for each input that shows no clear pattern that can be exploited. This makes them virtually impossible to reverse.
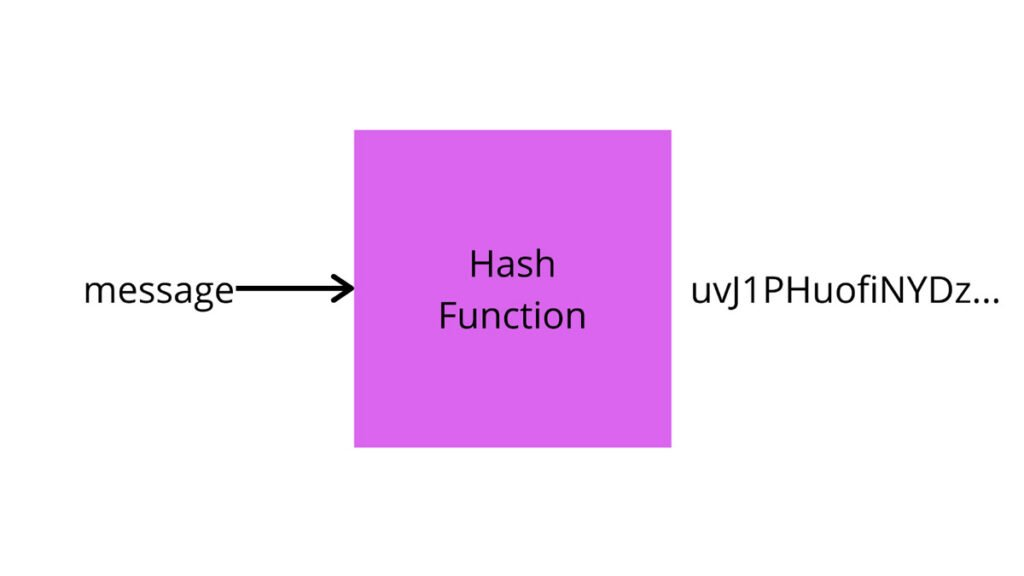
It is easy to generate a cryptographic hash from a given input, but impossible to generate the input from the hash. This means that if a client has the correct input, it can generate the cryptographic hash and compare its value to see if it has the correct input.
SSH uses hashes to verify the authenticity of messages. This is done using HMAC, or Hash-based Message Authentication Codes. This ensures that the received command is not tampered with in any way.
While the symmetric encryption algorithm is selected, a suitable message authentication algorithm is also selected. It works similarly to how the cipher is selected, as explained in the section on symmetric encryption.
Each transmitted message must contain a MAC, computed using the symmetric key, the packet sequence number, and the message content. It is sent outside the symmetrically encrypted data as the concluding section of the communication packet.
How does SSH work with these encryption techniques?
The way SSH works is to use a client-server model to enable the authentication of two remote systems and the encryption of data passing between them.
SSH operates on TCP port 22 by default (although this can be changed if necessary). The host (server) is listening on port 22 (or any other port assigned by SSH) for incoming connections. It sets up the secure connection by authenticating the client and opening the correct shell environment if the verification is successful.
The client must initiate the SSH connection by initiating the TCP handshake with the server, ensuring a secure symmetric connection, verifying whether the identity displayed by the server matches previous records (typically recorded in an RSA key archive file), and presenting the user credentials required to authenticate the connection.
There are two steps to establishing a connection: first, both systems must agree on encryption standards to protect future communications, and second, the user must authenticate. If the credentials match, the user is granted access.
Session encryption negotiation.
When a client attempts to connect to the server via TCP, the server presents the encryption protocols and the respective versions it supports. If the client has a matching protocol and version pair, an agreement is reached and the connection is initiated with the accepted protocol. The server also uses an asymmetric public key that the client can use to verify the authenticity of the host.
Once this is established, the two parties use what is known as the Diffie-Hellman key exchange algorithm to create a symmetric key. This algorithm allows both client and server to arrive at a shared encryption key that will henceforth be used to encrypt the entire communication session.
Here is how the algorithm works at a very simple level:
1.Both client and server agree on a very large prime number, which obviously has no common factor. This prime number value is also known as the seed value .
2.Next, the two parties agree on a common encryption mechanism to generate another set of values by manipulating the initialization values in a specific algorithmic way. These mechanisms, also known as cryptographic generators, perform large operations on the seed. An example of such a generator is AES (Advanced Encryption Standard).
3.Both parties independently generate another prime number. This is used as the secret private key for the interaction.
4.This newly generated private key, with the shared number and encryption algorithm (e.g., AES), is used to compute a public key that is distributed to the other computer.
5.The parties then use their own personal private key, the other machine’s shared public key, and the original prime number to create a final shared key. This key is calculated independently by both computers but will create the same encryption key on both sides.
6.Now that both sides have a shared key, they can symmetrically encrypt the entire SSH session. The same key can be used to encrypt and decrypt messages (read: section on symmetric encryption).
Now that the symmetrically protected encrypted session has been established, the user must be authenticated.
Authenticating the user
The final step before the user is granted access to the server is to authenticate his credentials. For this, most SSH users use a password. The user is asked to enter the username, followed by the password. These credentials pass securely through the symmetrically encrypted tunnel, so there is no chance of them being acquired by third parties.
Although passwords are encrypted, it is still not advisable to use passwords for secure connections. This is because many bots can simply brute force easy or default passwords and gain access to your account. Instead, the recommended alternative is SSH Key Pairs .
This is a set of asymmetric keys used to authenticate the user without the need to enter any password.
Conclusion
Gaining a thorough understanding of how SSH works can help users understand the security aspects of this technology. Most people consider this process to be extremely complex and incomprehensible, but it is much simpler than you think. If you are wondering how long it takes a computer to calculate a hash and authenticate a user, well, it happens in less than a second. In fact, the maximum amount of time is spent in transferring data over the Internet.
Hopefully, this SSH tutorial has helped you see the way different technologies can be put together to create a robust system in which each mechanism has a very important role to play. Also, you now know why Telnet became a thing of the past as soon as SSH appeared.